 |
|
|
 |
 |
|
|
| | 1 | 2 | 3 | 4 | 5 |
| 6 | 7 | 8 | 9 | 10 | 11 | 12 |
| 13 | 14 | 15 | 16 | 17 | 18 | 19 |
| 20 | 21 | 22 | 23 | 24 | 25 | 26 |
| 27 | 28 | 29 | 30 | 31 | |
|
|
| |
|
 |
 |
|
|
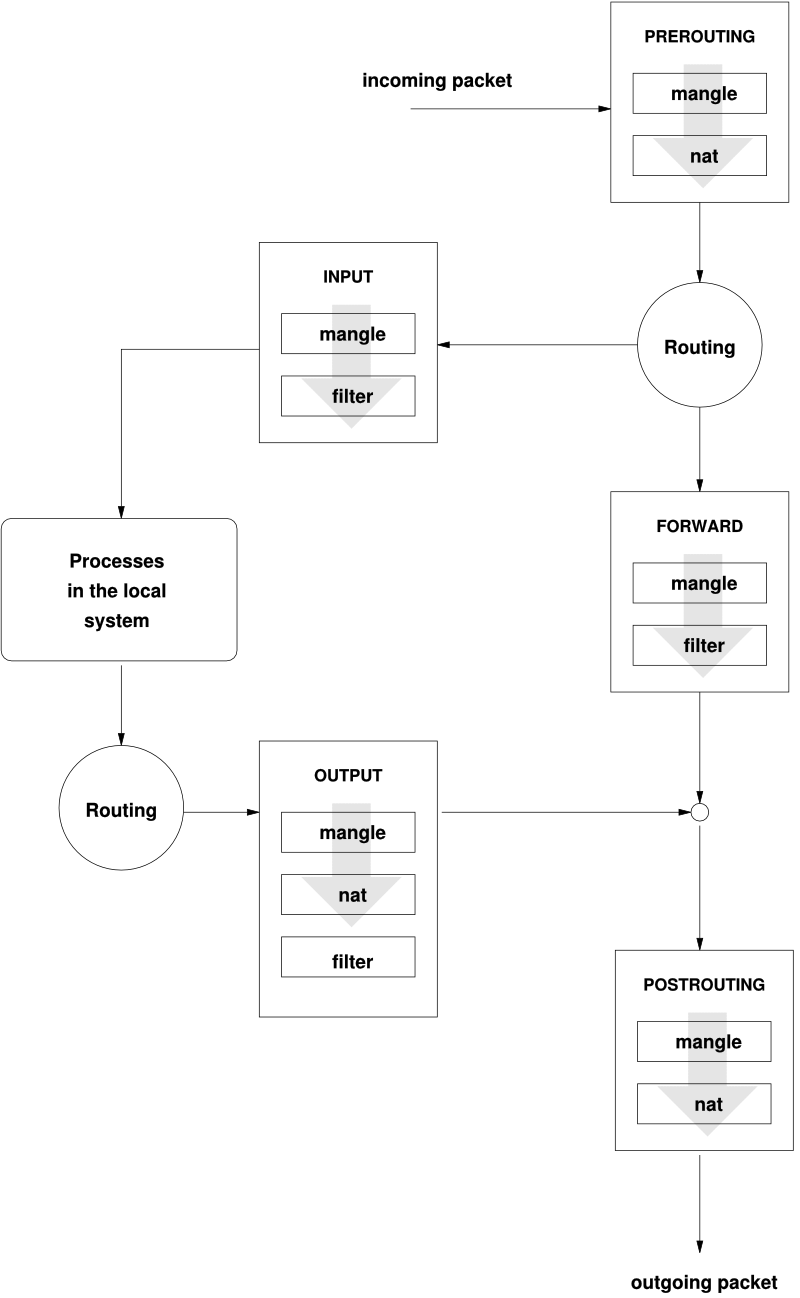
iptables ถึงเวลาต้องใช้ซะแล้ว
Thank you, Picture from => //linuxpoison.blogspot.com/2008/09/iptables-block-diagram.html
อ่านเจอก็ดีเหมือนกัน
Credit //www.sns.ias.edu/~jns/files/iptables_ruleset
อีกที่ๆ ละเอียดดี //www.linuxhomenetworking.com/wiki/index.php/Quick_HOWTO_:_Ch14_:_Linux_Firewalls_Using_iptables
ถ้าจะเปิดรับ รั่วๆ ไปเลย เอาไว้ทดสอบว่าถ้าไม่ผ่าน iptables แล้วมันใช้งานได้ไหม?
iptables -P INPUT ACCEPT
ต่อกันด้วยตัวอย่าง Firewall ที่มั่วเอง ลองดู
[root@pc ~]# cat /etc/Jenk_firewall
# iptables configuration file
# Flush all current rules from iptables
/sbin/iptables -F
/sbin/iptables -X
/sbin/iptables -Z
# Set default policies for INPUT, FORWARD and OUTPUT chains
/sbin/iptables --policy INPUT DROP
/sbin/iptables --policy FORWARD DROP
/sbin/iptables --policy OUTPUT ACCEPT
#Accept anything from myself
/sbin/iptables -A INPUT -i lo --jump ACCEPT
/sbin/iptables -A OUTPUT -o lo --jump ACCEPT
#Accept by Host/Network
/sbin/iptables -A INPUT -s 192.168.1.0/24 --jump ACCEPT
/sbin/iptables -A INPUT -s 11.22.33.44/32 --jump ACCEPT
#Block by Host/Network
/sbin/iptables -A INPUT -s 161.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 64.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 69.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 93.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 94.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 172.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 194.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 195.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 207.0.0.0/8 -j DROP
/sbin/iptables -A INPUT -s 203.206.0.0/16 -j DROP
/sbin/iptables -A OUTPUT -d 161.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 64.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 69.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 93.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 94.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 194.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 195.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 207.0.0.0/8 -j DROP
/sbin/iptables -A OUTPUT -d 203.206.0.0/16 -j DROP
/sbin/iptables -A INPUT -s 192.168.1.0/24 -p udp -m udp --dport 5060 -j ACCEPT
/sbin/iptables -A INPUT -s 11.22.33.44/32 -p udp -m udp --dport 5060 -j ACCEPT
#Client from TRUE ADSL
/sbin/iptables -A INPUT -s 58.8.0.0/16 -p udp -m udp --dport 5060 -j ACCEPT
/sbin/iptables -A INPUT -s 58.9.0.0/16 -p udp -m udp --dport 5060 -j ACCEPT
# RTP - the media stream
/sbin/iptables -A INPUT -p udp -m udp --dport 6000:20000 -j ACCEPT
#Block UDP Port 1000-1600
/sbin/iptables -A INPUT -p udp --dport 1000:1600 -j DROP
# Allow myself to be a non-passive FTP client
#/sbin/iptables -A INPUT -p tcp --dport ftp-data --jump ACCEPT
# Do not allow a local user to connect to a remote Telnet
# server and thus give away login and password information:
/sbin/iptables -A OUTPUT -p tcp --dport telnet --jump DROP
/sbin/iptables -A INPUT -p tcp --dport 5099:9999 --jump DROP
/sbin/iptables -A OUTPUT -p tcp --dport 5099:9999 --jump DROP
# Accept packets belonging to established and related connections
#/sbin/iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
#Protect DDOS
#/sbin/iptables -A INPUT -p tcp --syn -m limit --limit 1/s -j ACCEPT
#/sbin/iptables -A INPUT -p tcp --tcp-flags SYN,ACK,FIN,RST RST -m limit --limit 1/s -j ACCEPT
#/sbin/iptables -A INPUT -p tcp --syn -j DROP
#Protect Log Flood
/sbin/iptables -A INPUT -m limit --limit 10/minute --limit-burst 3 -j LOG --log-level DEBUG --log-prefix "Packet died: "
#TCP SSH port
/sbin/iptables -A INPUT -m state --state NEW -m tcp -p tcp -s 203.11.22.0/24 --dport 22 -j ACCEPT
/sbin/iptables -A INPUT -m state --state NEW -m tcp -p tcp -s 180.11.0.0/16 --dport 22 -j ACCEPT
#Protect SSH
/sbin/iptables -A INPUT -m recent --update --seconds 40 --hitcount 5 --name SSH --rsource -j DROP
/sbin/iptables -A INPUT -m recent --set --name SSH --rsource -j ACCEPT
#Service Mysql(Limit 3 IP)
/sbin/iptables -A INPUT -m state --state NEW -m tcp -p tcp --dport 3306 -j DROP
/sbin/iptables -A OUTPUT -p tcp --dport mysql -j DROP
#ICMP(Ping) - Allow All IP
#/sbin/iptables -A INPUT -m state --state NEW -m tcp -p icmp --icmp-type any -j ACCEPT
# Drop 1,2,6,7,15 not match in tables packet(only RHEL)
#Accept all pinging client
/sbin/iptables -A INPUT -p ICMP --icmp-type any -j ACCEPT
# No Answer for all ICMP Error
/sbin/iptables -A INPUT -p ICMP --icmp-type 0 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 3 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 4 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 5 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 8 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 9 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 10 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 11 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 12 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 13 -j DROP
/sbin/iptables -A INPUT -p ICMP --icmp-type 14 -j DROP
#Example Config
#/sbin/iptables -A INPUT -p udp --dport 53 -j ACCEPT
# Save settings with /sbin/service iptables save
# List iptables chains with 'iptables -L -v'
/sbin/iptables -P INPUT DROP
/sbin/iptables -P OUTPUT ACCEPT
/sbin/service iptables save
/sbin/iptables -L -v
[root@pc ~]#
ทดไว้เมื่อยามมีเวลา เดี๋ยวเวลารีบๆ จะได้หยิบฉวยทัน
** ยัง bug อยู่.. ค่อยๆ แก้ไป
| Create Date : 06 ธันวาคม 2552 |
| Last Update : 4 เมษายน 2554 9:58:10 น. |
|
0 comments
|
| Counter : 918 Pageviews. |
|
 |
|
|
|
|
|
| dokawa |
 |
|
|
 |
|